Tag: tools
-
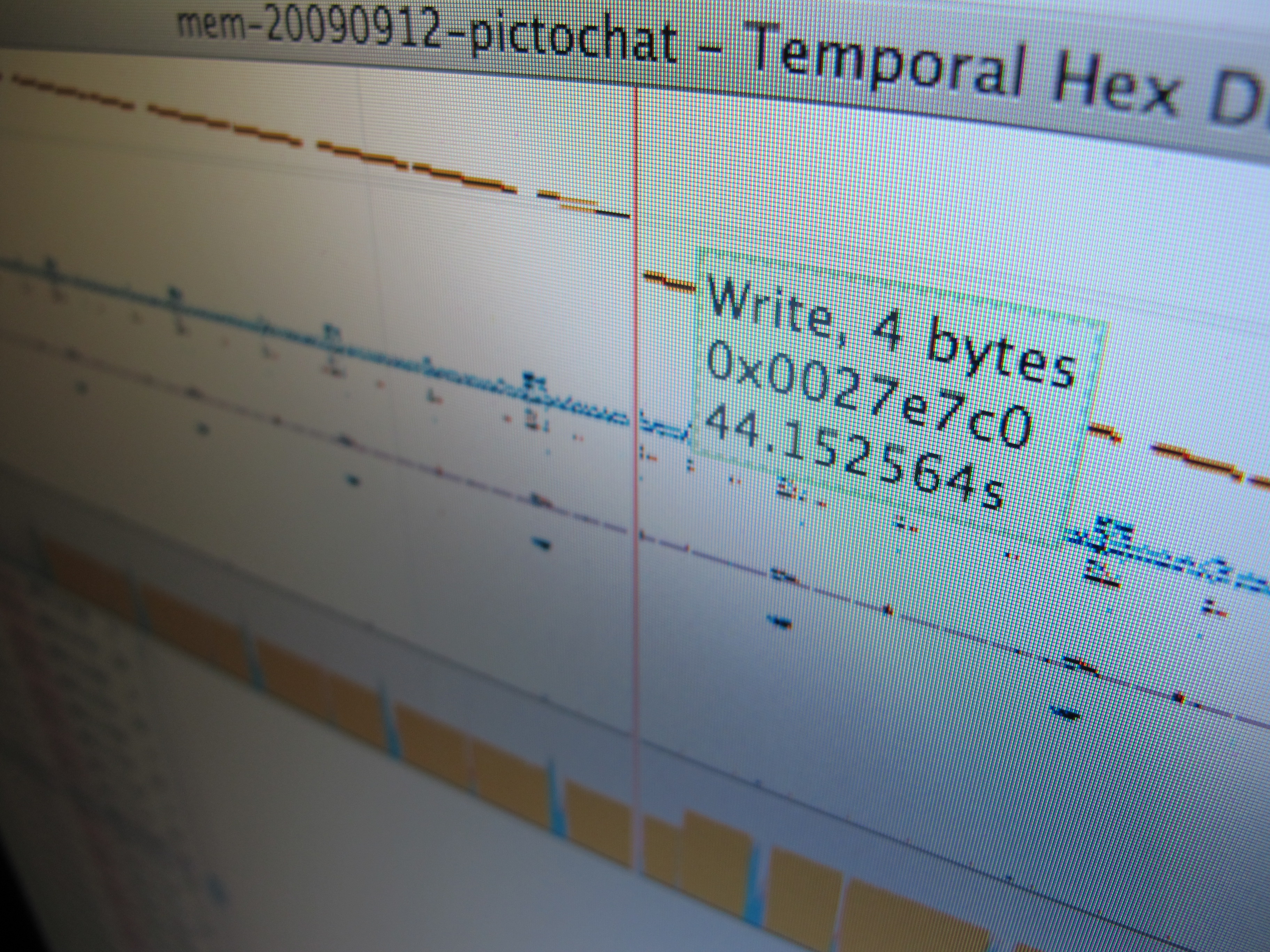
Temporal Hex Dump
After building some hardware to trace and inject data on the Nintendo DSi’s RAM bus, it became obvious pretty fast that there’s a lot of data there, and (as far as I know) no good tools for analyzing these sorts of logs. The RAM tracer has already given us a lot of insight into how…
-
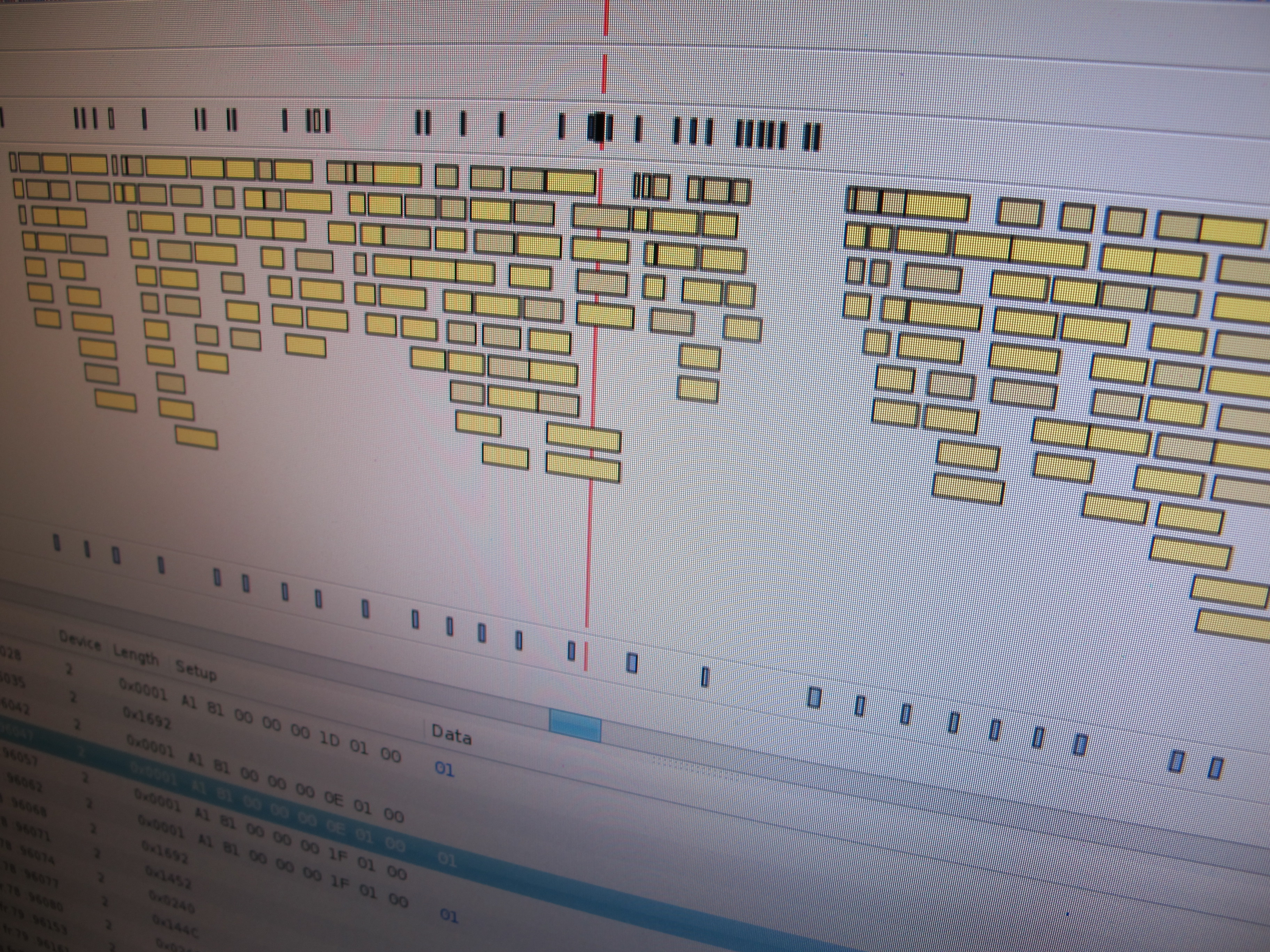
Virtual USB Analyzer
From late 2005 to early 2007, I worked on the USB virtualization stack at VMware. We ran into all sorts of gnarly bugs, many of which were very hard to reproduce or which required access to esoteric or expensive hardware. To help with debugging problems both internally and with customers in the field, we added…
-

Soft RFID tags and cuddly plushies
This week a new power tool arrived on my desk: How did this happen? It was actually kind of complicated… Months ago, Scott and I dreamed of an automated kegerator. For the workplace, naturally. We’d need some way to hand out credits that coworkers could use in order to dispense beer, so we’d need a…
-

New oscilloscope!
For a while now, I’ve been looking for a replacement for my ancient 50 MHz Hitachi analog scope. This scope has served me well for the 10+ years I’ve owned it, but it’s kind of a junker. Slow, out of calibration, flaky triggers… I’d could probably get a similar scope for about $15 on eBay.…
