Tag: user-interfaces
-
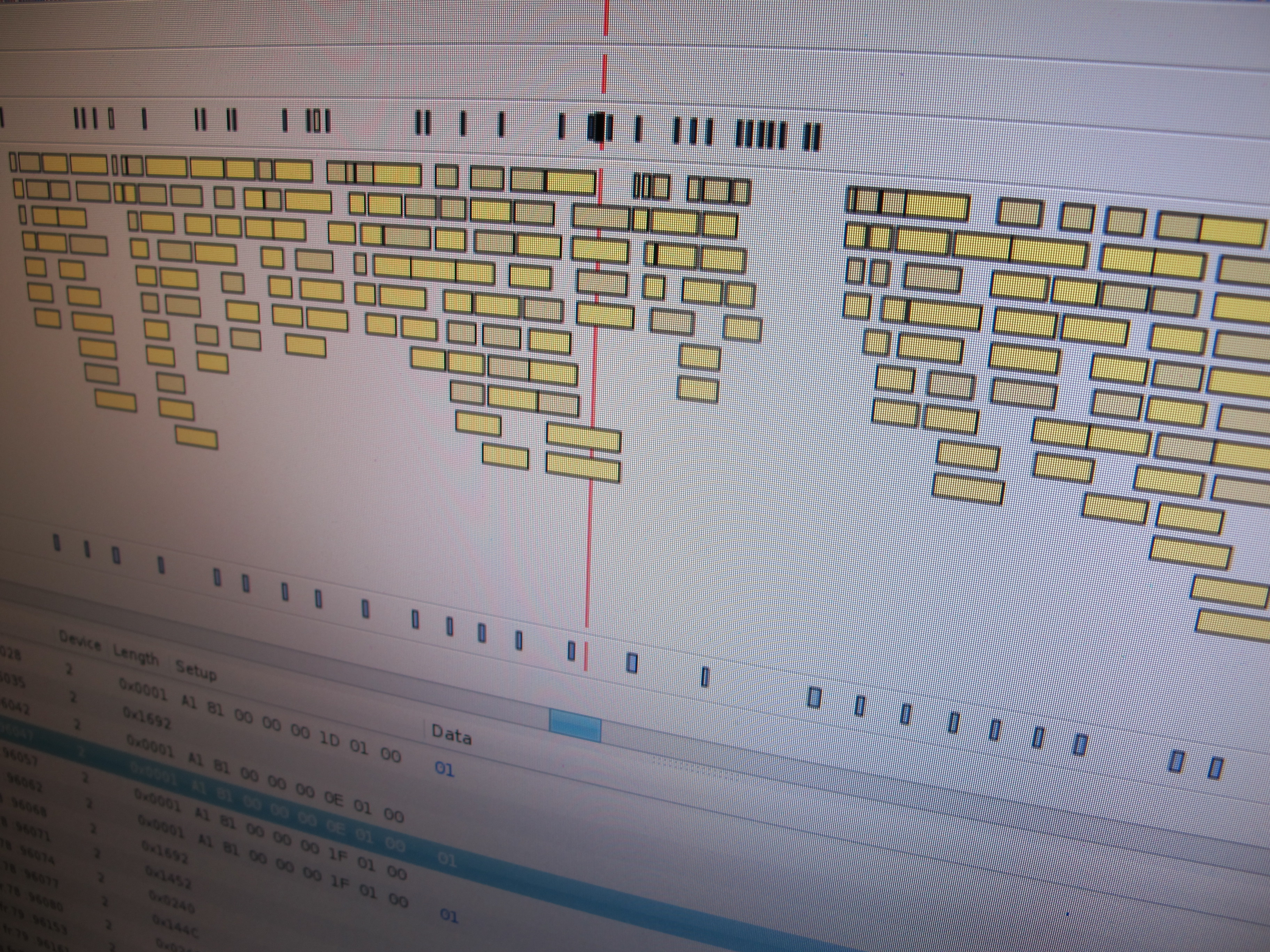
Virtual USB Analyzer
From late 2005 to early 2007, I worked on the USB virtualization stack at VMware. We ran into all sorts of gnarly bugs, many of which were very hard to reproduce or which required access to esoteric or expensive hardware. To help with debugging problems both internally and with customers in the field, we added…
-

Lego Sky
Over the weekend, I had a chance to finish up a project that I started (and immediately became distracted from) several weeks ago. In our house, Paul and I have a game room. This is where the video games live, as well as other assorted geekery. We have Magic cards, D&D books, some manga.. it’s…
