Tag: software
-
scanlime052 – Sewing Servo Mess
Finally debugging an old project. It’s a mess but we can work with this.
-
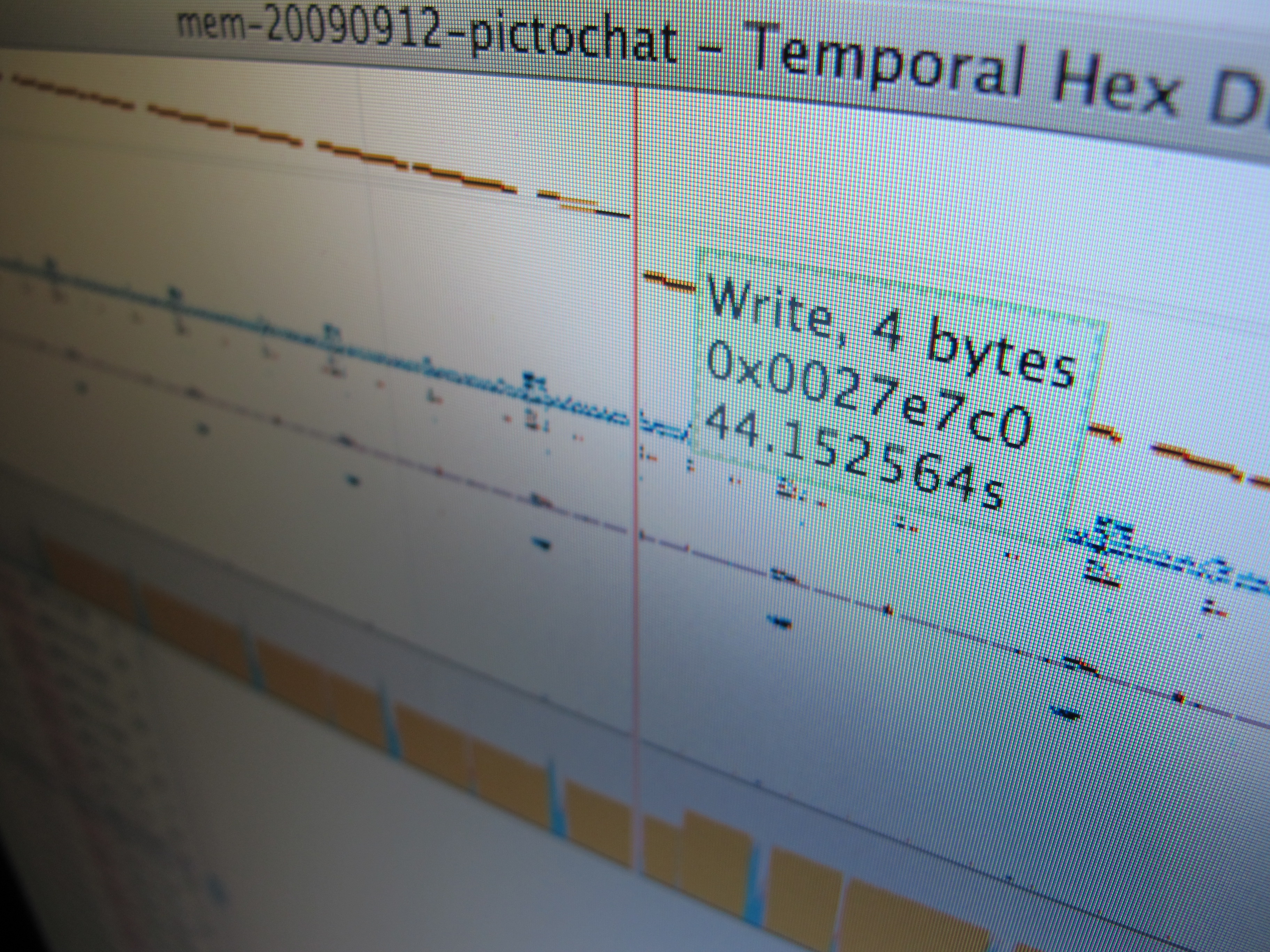
Temporal Hex Dump
After building some hardware to trace and inject data on the Nintendo DSi’s RAM bus, it became obvious pretty fast that there’s a lot of data there, and (as far as I know) no good tools for analyzing these sorts of logs. The RAM tracer has already given us a lot of insight into how…
-
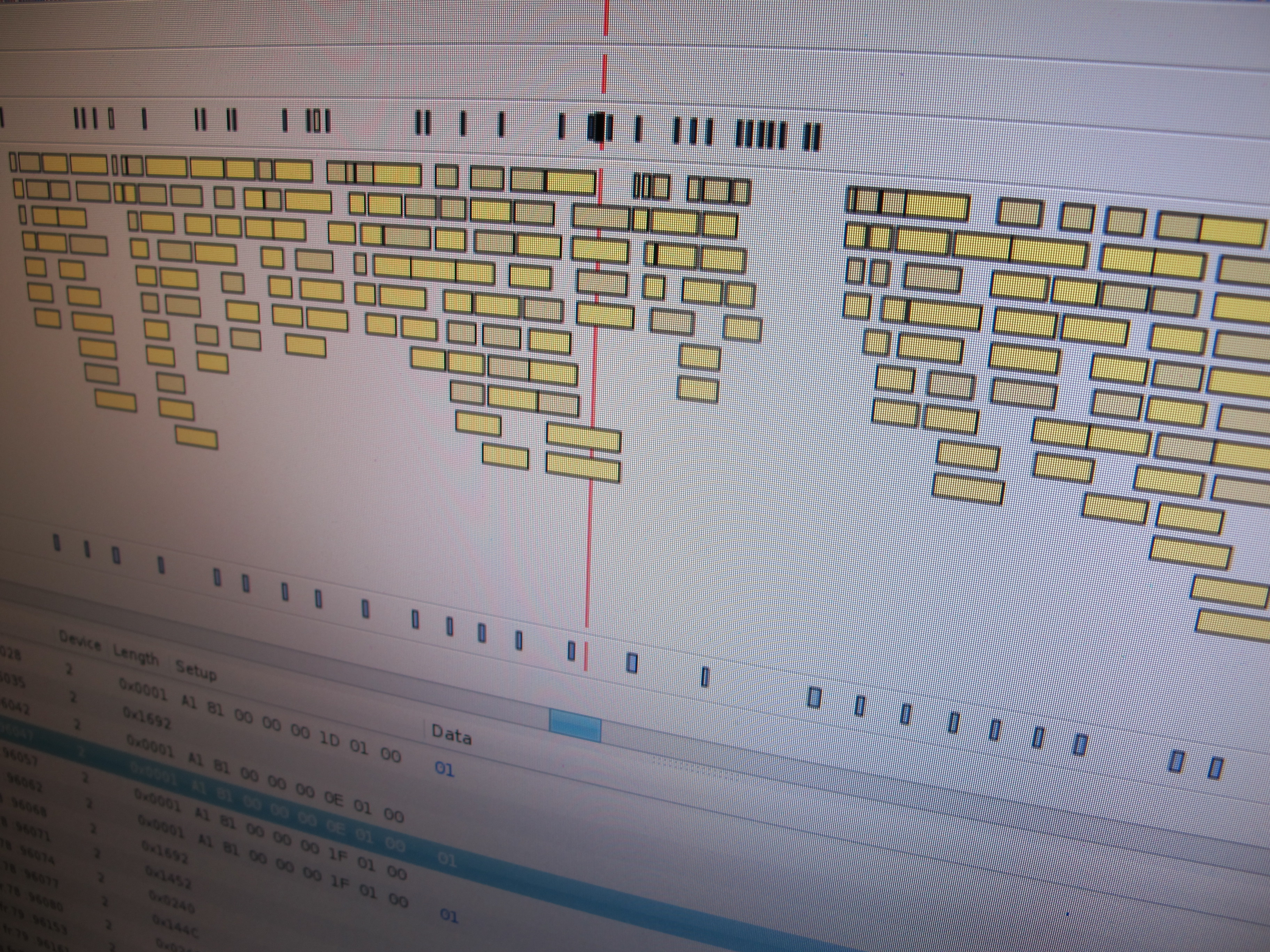
Virtual USB Analyzer
From late 2005 to early 2007, I worked on the USB virtualization stack at VMware. We ran into all sorts of gnarly bugs, many of which were very hard to reproduce or which required access to esoteric or expensive hardware. To help with debugging problems both internally and with customers in the field, we added…

